Tree vs Forest in Active Directory: Essential Differences Explained
Understanding the difference between Tree and Forest in Active Directory is crucial for network administrators and IT professionals managing Windows-based networks. These two components form the backbone of Active Directory's organizational structure, but they serve distinct purposes and operate at different hierarchical levels. Have you ever wondered why Microsoft designed this multi-tiered approach to network resource management? In this comprehensive guide, we'll explore the fundamental distinctions, applications, and relationships between these essential Active Directory components.
Understanding Active Directory Basics
Before diving into the specifics of Trees and Forests, it's worth taking a moment to understand what Active Directory actually is. Developed by Microsoft, Active Directory (AD) is a directory service that stores information about network objects such as users, computers, printers, and shared resources. It provides a centralized management system that enables administrators to organize these objects, control access, and implement security policies across an entire network infrastructure.
Active Directory uses a hierarchical structure that mimics the way organizations typically manage their resources. This structure allows for efficient organization of objects while maintaining logical boundaries between different parts of the network. I've seen many organizations struggle with AD implementation simply because they didn't properly understand the relationship between domains, trees, and forests. Trust me, getting this right from the start saves countless headaches down the road!
At its core, Active Directory is built around the concept of objects and containers. Objects represent network entities like users or computers, while containers (such as domains, organizational units, trees, and forests) help organize these objects in a way that reflects organizational structure. The directory information is stored in a database that resides on domain controllers, which are servers responsible for authentication and authorization processes within the network.
The primary building block of Active Directory is the domain, which represents a security boundary and administrative unit. Domains contain objects like user accounts and computers, and they define policies that apply to those objects. However, as organizations grow and their network requirements become more complex, they often need to extend beyond a single domain. This is where trees and forests come into play, providing mechanisms for organizing multiple domains while maintaining appropriate security boundaries.
What is a Tree in Active Directory?
A domain tree in Active Directory is essentially a collection of domains that share a contiguous namespace and are connected through trust relationships. Imagine a tree with its trunk and branches – this analogy closely resembles how domain trees are structured in AD. The first domain created becomes the root domain (the trunk), and additional domains (the branches) can be added underneath it to form a hierarchical structure.
For example, if a company has a root domain named "company.com," they might create child domains like "sales.company.com" or "it.company.com" to organize different departments. Each of these domains maintains its own distinct identity but remains part of the overall tree structure. This approach allows for departmental autonomy while preserving a unified management framework.
One of the most important characteristics of a tree is the transitive trust relationship that exists between domains. When domains are part of the same tree, they automatically establish two-way transitive trusts. This means that if Domain A trusts Domain B, and Domain B trusts Domain C, then Domain A automatically trusts Domain C. These trust relationships enable users in one domain to access resources in another domain within the same tree without requiring separate authentication.
Another key aspect of trees is the contiguous namespace. All domains within a tree share a common DNS (Domain Name System) namespace. This creates a continuous naming structure where each child domain's name includes its parent domain's name. For instance, if "company.com" is the parent domain, then "marketing.company.com" would be a child domain within that tree. This naming convention clearly indicates the hierarchical relationship between domains and simplifies DNS management.
What is a Forest in Active Directory?
While a tree represents a collection of domains with a contiguous namespace, a forest takes this organizational structure to the next level. An Active Directory forest is a complete instance of Active Directory that contains one or more domain trees. These trees may or may not share a contiguous namespace, which provides greater flexibility in combining different organizational structures.
The first domain created in a forest becomes the forest root domain. This domain plays a critical role as it houses the schema master – a special role that controls modifications to the directory schema (the definition of all object types and attributes that can exist in the directory). The forest root domain also contains the enterprise admins and schema admins groups, which have privileges that extend throughout the entire forest.
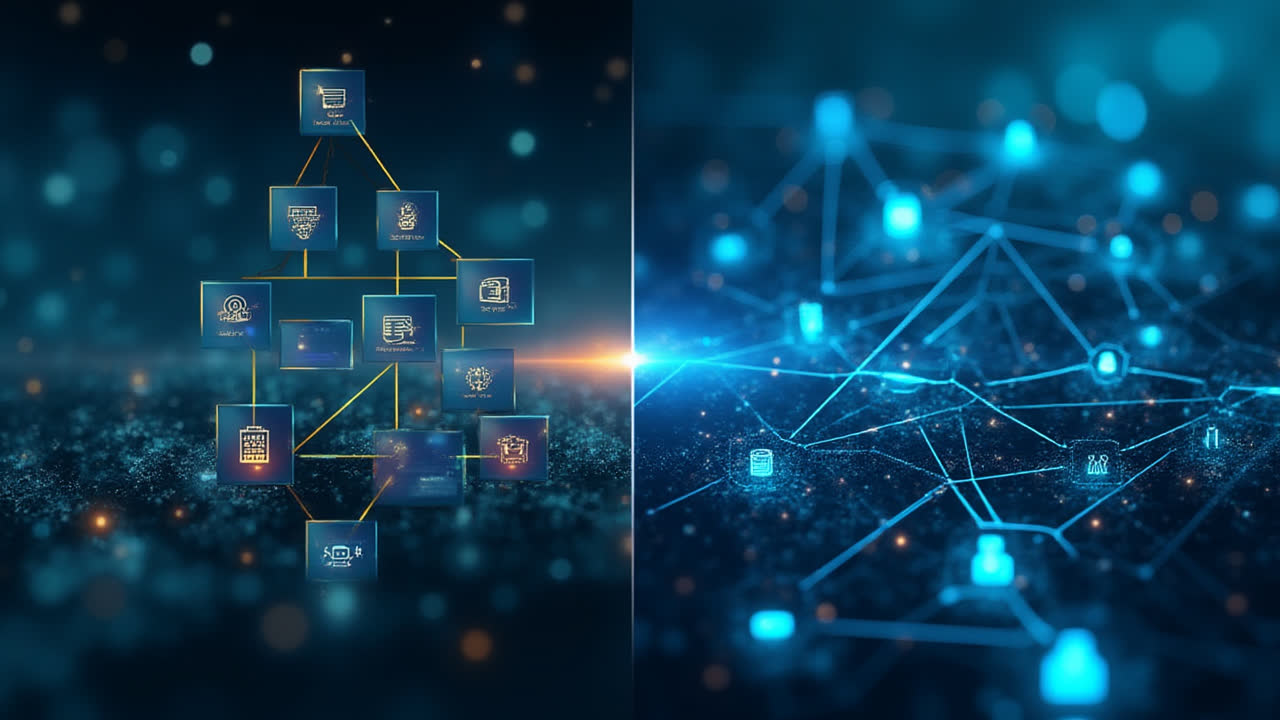
Forests serve as the ultimate security boundary in Active Directory. While domains within a tree automatically trust each other through transitive trust relationships, separate trees within a forest do not necessarily share the same trust relationship by default. However, all domains within a forest share a common schema, configuration, and global catalog. The global catalog is a partial replica of all objects in the forest that facilitates searches across domain boundaries.
Organizations might create multiple forests when they need complete isolation between different parts of their network infrastructure. For example, a company might maintain separate forests for its production environment and its development/testing environment. Similarly, when companies merge or acquire other businesses, they might initially maintain separate forests until they can develop a unified directory structure.
It's worth noting that while forests provide strong security boundaries, they can communicate with each other through forest trust relationships. These trust relationships must be explicitly established by administrators and can be configured to allow specific types of resource access across forest boundaries. In my experience working with large enterprises, properly configured forest trusts are essential for businesses that need to maintain separate administrative domains while enabling limited collaboration.
Key Differences Between Tree and Forest in Active Directory
Now that we understand what trees and forests are in the context of Active Directory, let's examine the key differences between these two organizational structures. These distinctions are crucial for designing and implementing an effective Active Directory infrastructure.
| Comparison Point | Tree in Active Directory | Forest in Active Directory |
|---|---|---|
| Definition | A collection of domains that share a contiguous namespace | A complete Active Directory instance containing one or more trees |
| Namespace | All domains share a contiguous DNS namespace | May contain multiple trees with different namespaces |
| Trust Relationships | Automatic two-way transitive trusts between domains | Trees within a forest may require explicit trust relationships |
| Security Boundary | Limited security boundary (domains still share schema) | Ultimate security boundary in Active Directory |
| Schema | Shares schema with other domains in the tree | All domains within the forest share a common schema |
| Administrative Scope | Domain administrators manage their specific domains | Enterprise admins have privileges across the entire forest |
| Typical Use Case | Departmental divisions within an organization | Separate business units or company acquisitions |
| Creation Process | Created by adding child domains to a parent domain | Created by establishing the first domain (forest root) |
Practical Applications and Considerations
Understanding the theoretical differences between trees and forests is important, but how does this knowledge translate to practical network management? Let's explore some real-world applications and considerations for implementing trees and forests in Active Directory.
When to Use Domain Trees
Domain trees are ideal when an organization wants to maintain a hierarchical structure while preserving a unified namespace. Here are some scenarios where implementing domain trees makes sense:
- Departmental Separation: Large organizations often create separate domains for different departments like HR, Finance, or IT, allowing for departmental autonomy while maintaining connectivity.
- Geographic Distribution: Companies with offices in multiple locations might create domain trees to accommodate regional differences in policies or compliance requirements.
- Decentralized Administration: When different teams need to manage their own users and resources independently, domain trees provide administrative boundaries while preserving a common identity structure.
When to Implement Forests
Forests provide stronger separation and are appropriate in scenarios that require more rigorous security boundaries. Consider implementing multiple forests in these situations:
- Mergers and Acquisitions: When companies merge, maintaining separate forests initially can ease the transition while longer-term integration strategies are developed.
- Strict Regulatory Compliance: Organizations that deal with different regulatory frameworks might isolate affected systems in separate forests to prevent compliance issues from affecting the entire network.
- Development/Testing Environments: To protect production environments, many organizations create separate forests for development and testing.
- High-Security Zones: Networks containing highly sensitive information might be isolated in separate forests to minimize the risk of unauthorized access.
Frequently Asked Questions
Can a forest contain multiple trees with different namespaces?
Yes, one of the key advantages of a forest is that it can contain multiple domain trees with different DNS namespaces. For example, a single forest might contain both "company.com" and "enterprise.org" as separate domain trees. This flexibility is particularly useful in scenarios involving mergers and acquisitions, where organizations need to preserve existing domain names while establishing a unified directory infrastructure. Each tree maintains its own namespace hierarchy, but they all share common schema, configuration, and global catalog services within the forest.
How do trust relationships differ between trees and forests?
Trust relationships operate differently within and between trees and forests. Within a domain tree, two-way transitive trusts are automatically established between parent and child domains. This means that if Domain A trusts Domain B, and Domain B trusts Domain C, then Domain A inherently trusts Domain C. In contrast, separate trees within a forest do not automatically establish transitive trusts with each other. Forest trusts, which connect entire forests, must be explicitly configured by administrators and can be set up as one-way or two-way trusts, depending on the specific requirements. These trust relationships determine how authentication works across domain and forest boundaries.
What happens to the Active Directory structure when a company acquires another organization?
When a company acquires another organization, there are several approaches to integrating the Active Directory infrastructures. Initially, the most common approach is to establish a forest trust between the existing Active Directory forests of both companies. This allows immediate resource sharing while maintaining separation. Over time, the organizations might choose to merge the directories completely, which could involve migrating objects from one forest to another, creating a new forest to replace both existing ones, or restructuring into a new tree within an existing forest. The chosen approach depends on factors such as the size of the organizations, security requirements, compliance needs, and long-term business strategy. Tools like Microsoft's Active Directory Migration Tool (ADMT) can facilitate this transition.
Conclusion: Making the Right Choice for Your Network
The distinction between trees and forests in Active Directory represents more than just technical terminology—it reflects fundamental decisions about how to structure an organization's network resources. Trees provide a way to organize domains within a contiguous namespace, creating a hierarchical structure that balances centralized management with departmental autonomy. Forests, as collections of trees, establish the ultimate security boundaries in Active Directory and enable organizations to manage complex network environments with distinct administrative domains.
When designing an Active Directory infrastructure, network administrators must carefully consider their organizational requirements, security needs, and long-term growth strategies. In smaller organizations with straightforward structures, a single domain or domain tree might be sufficient. Larger enterprises with complex organizational structures or stringent security requirements might benefit from implementing multiple forests connected through strategic trust relationships.
Remember that Active Directory structures can be difficult to change once implemented, so thorough planning is essential. By understanding the differences between trees and forests and their respective applications, you'll be better equipped to design an Active Directory infrastructure that supports your organization's needs both now and in the future.